- support@raidefend.com
- Mon - Sat: 9.00 am - 6.00 pm


VAPT Services in Dubai
Raidefend's VAPT services in Dubai combine vulnerability assessment with penetration testing to expose and eliminate security weaknesses across your networks, applications, cloud, and APIs — before attackers exploit them.
1000+Vulns Found
98%Fix Rate
48hrReport Delivery
24/7Support
Scan Complete14 vulns identified
Exploit TestedSQLi confirmed
Report ReadyPrioritised fixes
800 48 2273Toll-Free Helpline
Dubai, UAEHeadquartered & Serving
raidefend.comVisit Our Website
support@raidefend.comDrop Us a Line


Dual-Layered Security
Vulnerability Assessment + Penetration Testing combined
1000+Vulns Found
98%Fix Rate
48hrReports
about vapt
Unmask & Mitigate Security Risks with VAPT in Dubai
Vulnerability assessment and penetration testing is crucial in today's evolving threat landscape where new methods are constantly developed to exploit weaknesses. Raidefend offers advanced VAPT solutions — a dual-layered approach that combines continuous vulnerability scanning with real-world attack simulation to solidify the security of your digital infrastructure.
01
Vulnerability Assessment
Continuous scanning using latest exploit databases to identify weaknesses across your networks, applications, and systems before attackers find them.
02
Penetration Testing
Simulation of real-world attacks using sophisticated hacking techniques to evaluate the actual risk level of each identified vulnerability.
03
Risk Prioritisation
Vulnerabilities categorised by severity with clear, prioritised remediation roadmaps — so your team fixes what matters most first.
04
Remediation Verification
Post-fix re-testing to verify that identified vulnerabilities have been properly addressed and security controls are effectively implemented.
vapt process
Steps Involved in VAPT Implementation
A structured, six-phase methodology that takes you from scoping through to verified remediation — ensuring nothing is missed.
Planning & Scoping
We define the specific needs of your VAPT engagement — testing methods, compliance priorities, scope boundaries, and areas to be assessed — ensuring a focused and effective security evaluation.
- Define testing scope and boundaries
- Identify compliance requirements (ISO 27001, PCI-DSS, UAE Cybercrime Law)
- Select testing methodologies (black-box, grey-box, white-box)
- Establish rules of engagement and communication protocols


Planning Phase
Information Gathering
Extensive investigation and consultation to gather intelligence about target systems, network architecture, application landscape, and potential weaknesses.
- Network topology and architecture mapping
- Application and API inventory
- Open-source intelligence (OSINT) gathering
- Technology stack fingerprinting


Gather Phase
Vulnerability Assessment
Potential vulnerabilities in applications and target systems are scanned using automated tools and manual techniques — mapping the full attack surface.
- Automated vulnerability scanning with latest exploit databases
- Manual verification to eliminate false positives
- OWASP Top 10 and SANS Top 25 coverage
- Configuration and patch-level analysis
Assess Phase
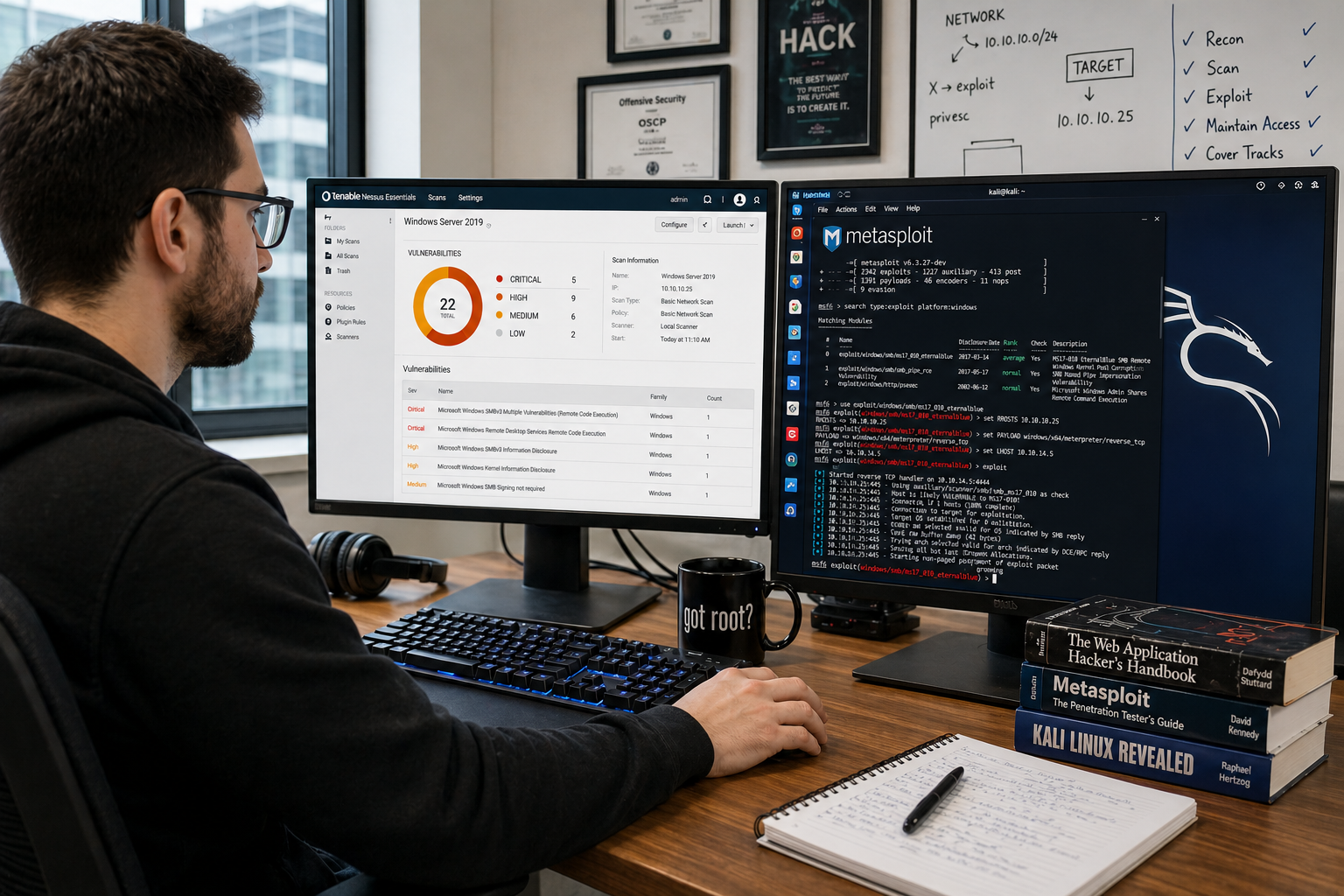
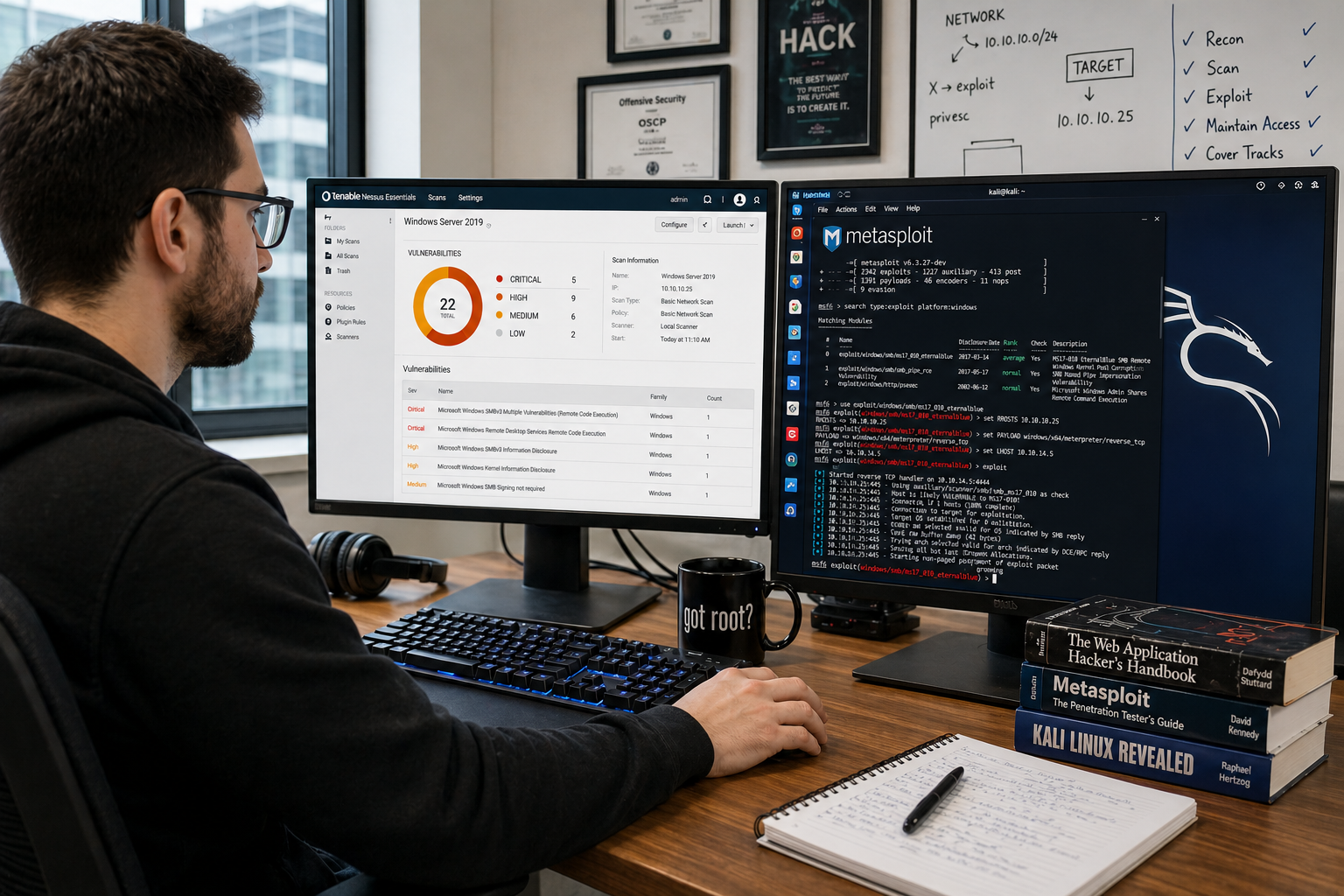
Exploitation & Penetration Testing
Our certified ethical hackers execute real-world attacks on identified vulnerabilities using advanced hacking techniques to assess the actual potential risk.
- SQL injection, XSS, CSRF, and business logic attacks
- Privilege escalation and lateral movement testing
- Authentication bypass and session hijacking attempts
- Evidence-based exploitation with proof of concept


Exploit Phase
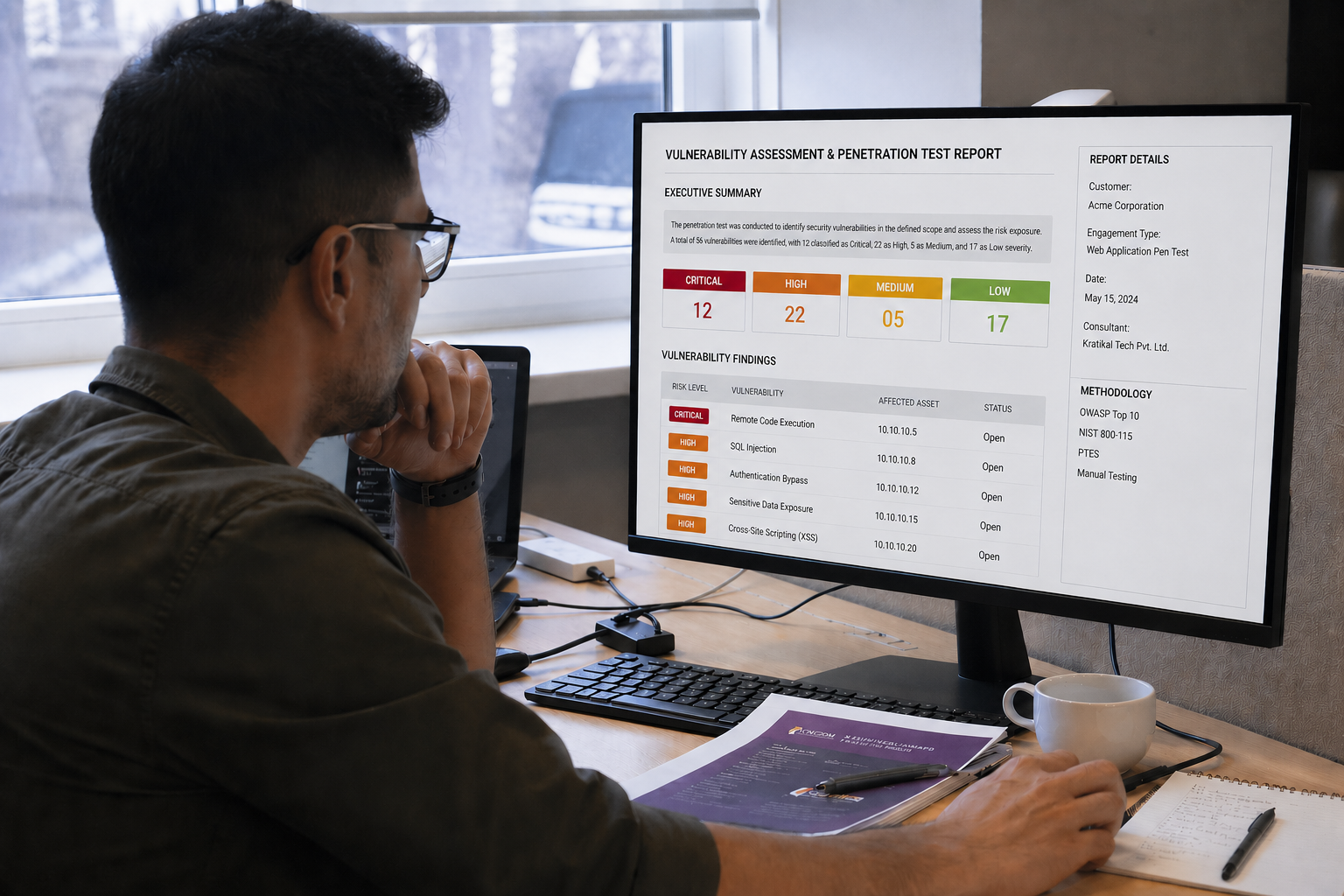
Reporting & Remediation
Detailed reports with risk-rated findings, evidence of exploits, executive summaries, and step-by-step remediation recommendations prioritised by severity.
- Executive summary for leadership teams
- Technical findings with severity ratings (Critical/High/Medium/Low)
- Step-by-step remediation guidance for each vulnerability
- Compliance documentation for ISO 27001, PCI-DSS, NESA
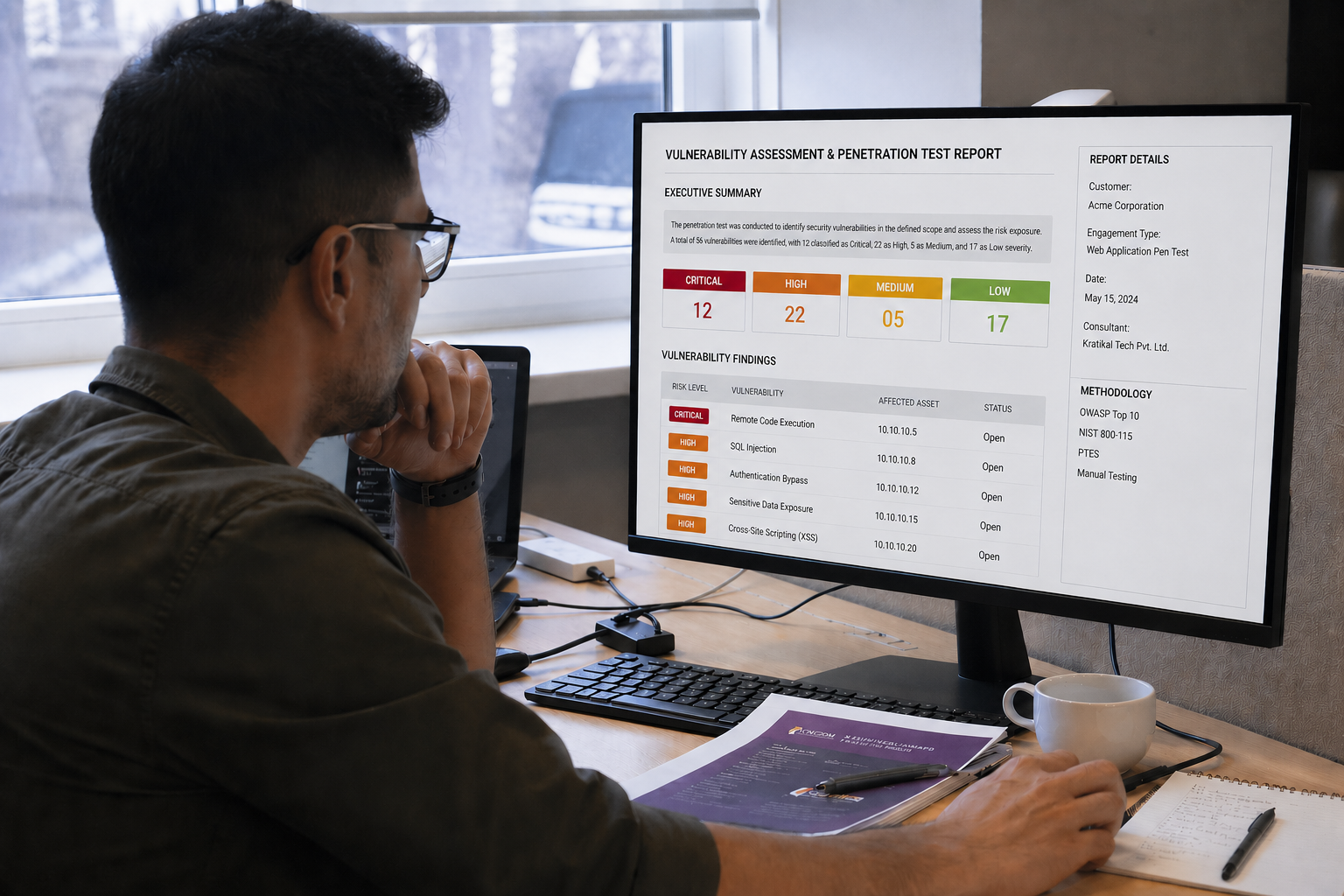
Report Phase
Remediation Verification
After your team implements the fixes, we re-test to verify that identified vulnerabilities have been properly addressed and appropriate security controls are in place.
- Re-testing of all critical and high-severity findings
- Verification that patches and fixes are effective
- Updated compliance certification documentation
- Final sign-off and security clearance report


Verify Phase
vapt solutions
In-depth Security Assessment with Raidefend's VAPT Solutions
Raidefend goes beyond the basics — our comprehensive suite of VAPT solutions identifies and determines the severity of vulnerabilities across every layer of your digital infrastructure.
Organisational Penetration Testing
Exploitation of every layer of your IT infrastructure — cloud, APIs, networks, applications, and physical security — for a complete organisational view.
Learn MoreNetwork Penetration Testing
Real-world attacks across your network to identify vulnerabilities with detailed analysis and recommendations for strengthening defences.
Learn MoreWeb Application Penetration Testing
Exploitation involving SQL injection, XSS, CSRF, and business logic flaws to identify web application vulnerabilities in advance.
Learn MoreMobile Penetration Testing
Static and dynamic analysis of iOS and Android applications to detect vulnerabilities that threaten data security and system integrity.
Learn MoreAPI Penetration Testing
Automated and manual exploitation of APIs to expose authentication, IDOR, injection, and authorisation vulnerabilities.
Learn MoreCloud Penetration Testing
Attacks against cloud configurations, data storage, APIs, and access controls on AWS, Azure, and GCP to prevent potential breaches.
Learn More

Proactive Defence
Find and fix vulnerabilities before attackers exploit them
98%Fix Rate
0Breaches
advantages
Advantages of VAPT Services in Dubai
VAPT is more than a routine security check — it's a strategic investment that strengthens your entire security posture.
Uncover Hidden Vulnerabilities
Expert analysts meticulously examine networks, applications, and systems to find weaknesses before attackers do.
Prioritise Risks
Vulnerabilities categorised by severity, helping you focus remediation efforts on the most critical issues first.
Strengthen Security Posture
Proactively address vulnerabilities to reduce the risk of data breaches and costly operational downtime.
Ensure Regulatory Compliance
Meet UAE Cybercrime Law, ISO 27001, PCI-DSS, NESA, and industry-specific security regulations.
Build Customer Trust
Demonstrating commitment to cybersecurity enhances your reputation and instils confidence in customers and partners.
Cost Efficiency
Addressing vulnerabilities early and maintaining compliance prevents financial losses from breaches and legal issues.
why raidefend
Why Choose Raidefend for VAPT in Dubai
Certified security professionals with a proven track record of identifying and mitigating vulnerabilities across diverse industries.
01
Certified Ethical Hackers
Our team holds CISSP, CEH, OSCP, and CompTIA Security+ certifications — delivering expert-level penetration testing every time.
02
Tailored Assessments
Every VAPT engagement is designed around your specific needs and risk profile — no cookie-cutter packages.
03
Transparent Communication
We work closely with your team throughout the entire VAPT process, providing clear updates and timely support.
04
Latest Threat Intelligence
Our knowledge stays current with the latest cyber threats — protecting you from even the most advanced attacks.
05
Compliance Documentation
VAPT reports include compliance evidence for ISO 27001, PCI-DSS, UAE Cybercrime Law, and industry regulations.


technology partners
Powered by Industry Leaders
Fortinet
SentinelOne
Sophos
Trend Micro
Microsoft
HackTheBox
KnowBe4
Teramind
Fortinet
SentinelOne
Sophos
Trend Micro
Microsoft
HackTheBox
KnowBe4
Teramind
1000+Vulnerabilities Found
98%Remediation Rate
48hrReport Turnaround
24/7Security Support
our clients
We are Trusted Worldwide
Hear what our clients say about our VAPT services and security assessments.
“
Raidefend's VAPT team identified critical vulnerabilities in our web applications that our internal team had missed. The report was clear, actionable, and delivered in 48 hours. Exceptional work.
KA
Khalid Al Maktoum
Head of IT Security
“
Their penetration testing helped us achieve ISO 27001 compliance ahead of schedule. The remediation verification phase gave us complete confidence that our fixes were effective.
PS
Priya Sharma
CISO
“
We engaged Raidefend for a full organisational pen test — cloud, APIs, network, and applications. Their ethical hackers found vulnerabilities we didn't know existed. Highly recommend.
DW
David Wilson
CTO
common questions
Frequently Asked Questions
How often should VAPT be conducted?
We recommend conducting VAPT at least annually, or more frequently if your organisation handles sensitive data, experiences significant technology changes, or operates in a regulated industry. Many clients opt for quarterly assessments for continuous protection.
Is VAPT safe for our production systems?
Yes. Raidefend's certified ethical hackers conduct VAPT with the utmost care and professionalism. We follow strict rules of engagement agreed during the planning phase, ensuring your systems are not harmed during the assessment. Testing can also be scheduled during off-peak hours.
What happens if vulnerabilities are discovered?
Our detailed reports outline every vulnerability found, along with its potential impact, severity rating, and recommended remediation steps. We can also assist your team in implementing fixes and then re-test to verify they're effective.
Can VAPT help us achieve compliance?
Absolutely. Our VAPT services are designed to meet various industry-specific security standards including ISO 27001, PCI-DSS, UAE Cybercrime Law (Federal Law No. 5 of 2012), NESA, and GDPR requirements.
How long does a VAPT engagement take?
The duration depends on the scope of the engagement — a single web application may take 3-5 days, while a full organisational pen test could take 2-4 weeks. We consult with you to define a realistic timeframe during the planning phase.
What types of testing methodologies do you use?
We offer black-box testing (no prior knowledge), grey-box testing (partial knowledge), and white-box testing (full access) — selected based on your objectives, risk profile, and compliance requirements.
What is the difference between vulnerability assessment and penetration testing?
A vulnerability assessment identifies and catalogues security weaknesses across your systems using automated scanners and manual review. Penetration testing goes a step further by actively exploiting those vulnerabilities to determine real-world impact. Together, they provide a complete picture of your security posture.
Do you provide a re-test after remediation?
Yes. After your team addresses the identified vulnerabilities, we conduct a focused re-test to verify that all fixes have been properly implemented and no new issues have been introduced. A re-test report with updated findings is provided upon completion.
What certifications do your VAPT team members hold?
Our security professionals hold industry-recognised certifications including CEH (Certified Ethical Hacker), OSCP (Offensive Security Certified Professional), CREST, GPEN, and CISSP. This ensures our assessments meet the highest professional standards.
Will VAPT cause any downtime to our systems?
Our testing methodology is designed to minimise any disruption. We carefully plan the scope and intensity of tests, and critical or potentially disruptive tests are scheduled during maintenance windows or off-peak hours. In most cases, there is zero downtime.
What types of assets can be tested?
We test a wide range of assets including web applications, mobile applications (iOS and Android), APIs, cloud infrastructure (AWS, Azure, GCP), internal and external networks, wireless networks, IoT devices, and thick-client applications.
How do you ensure confidentiality of our data during testing?
We sign a Non-Disclosure Agreement (NDA) before every engagement. All findings and data collected during the assessment are handled with strict confidentiality, encrypted in transit and at rest, and securely destroyed after the agreed retention period.
What deliverables do we receive after the VAPT?
You receive a comprehensive report that includes an executive summary for leadership, detailed technical findings with evidence (screenshots and proof-of-concept), risk ratings based on CVSS scoring, prioritised remediation recommendations, and a compliance mapping summary where applicable.
Can VAPT be performed on cloud-hosted applications?
Yes. We regularly perform VAPT on cloud-hosted environments across AWS, Microsoft Azure, and Google Cloud Platform. We work within the shared responsibility model and follow each provider's penetration testing policies to ensure full compliance during the assessment.
How much does a VAPT engagement cost?
Pricing depends on several factors including the number and type of assets to be tested, the depth of testing required, and the complexity of your environment. We provide a customised quote after an initial scoping discussion to ensure you get exactly what you need — contact us for a free consultation.
Ready to Expose Your System Vulnerabilities?
Don't wait for a breach to discover your security gaps. Contact Raidefend today for a comprehensive VAPT assessment and secure your digital infrastructure.
Get Free VAPT Consultation